|
GajShield Data Security Firewall
A Firewall That Understands Your DataA leap ahead of the traditional Next Last Generation firewall. The Data Security Firewall takes a Data First Approach — understanding your organization's data, providing deeper data-level visibility, and controlling the data threat surface to prevent exploitation. Download Brochure ↓ Request a Demo |

|
A Multi-Step Process Towards Data Security
From application identification to policy enforcement, every data transaction passes through four layers of intelligent inspection.
|
01
Application IdentificationIdentifies the application in use and detects context points within it — login ID, sender, recipients, subject, body, attachments, and more. |
02
Contextual Data ClassificationBreaks down the packet into multiple data points using the Contextual Intelligence Engine, creating a structured form for security policies. |
03
Visibility & Policy EnforcementValidates parameters against data security policies, checks behavioural anomalies via UEBA, and applies granular controls on each packet. |
04
Protect & ReportTakes appropriate action to prevent data exploitation, records every event, and generates detailed violation reports for security teams. |
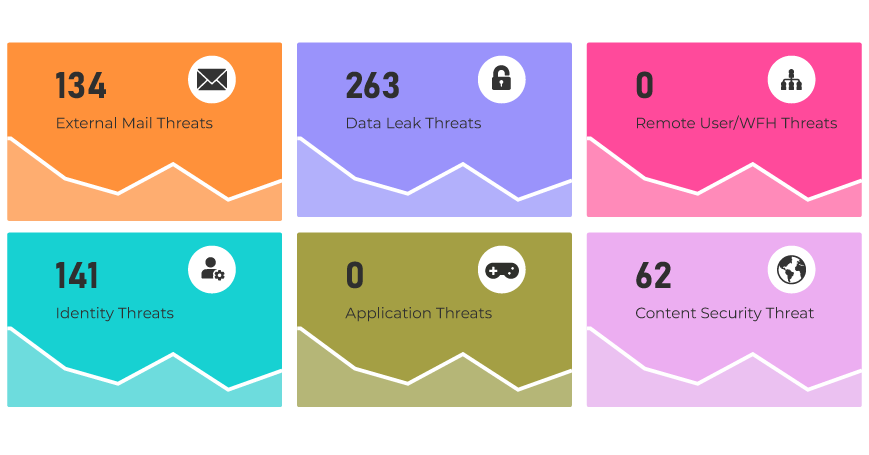
At-A-Glance Control Over Your Data Health
A unique, powerful dashboard that gives enterprises a complete overview of data threats and overall data health — powered by GajOS Bulwark's granular reporting and intelligence from the Contextual Intelligence Engine.

Threat Plane Overview
|
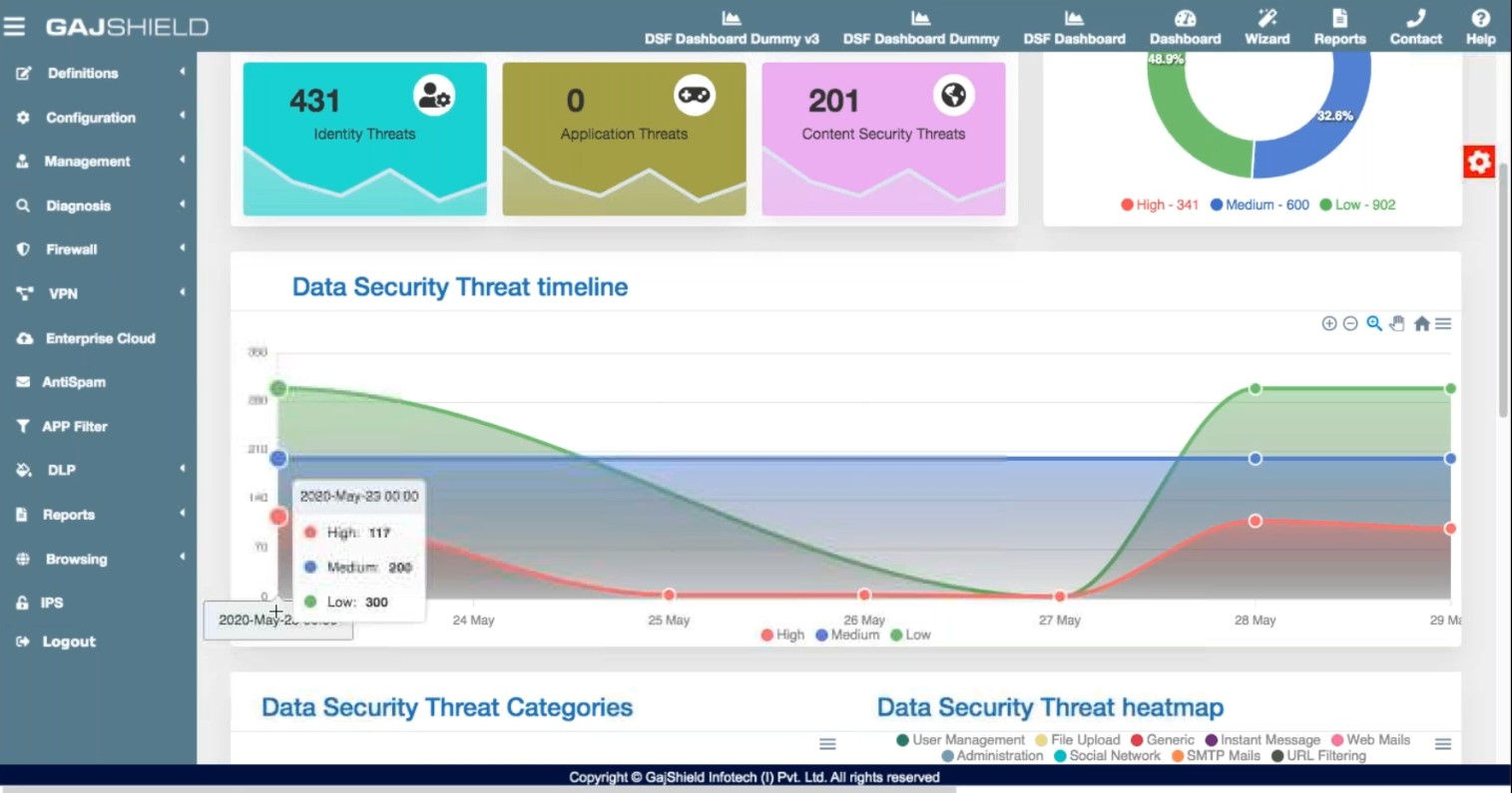
Threat Categories
|

Security Health
|
Quick Response
|
|
Data Criticality Health Indicator
Prioritise What Matters MostAssign violation criticality levels to every facet of your Data Security Policies. Prioritise remediation efforts by severity, direct resources toward the most critical issues first, and maintain a proactive, resilient security posture. |

|
|
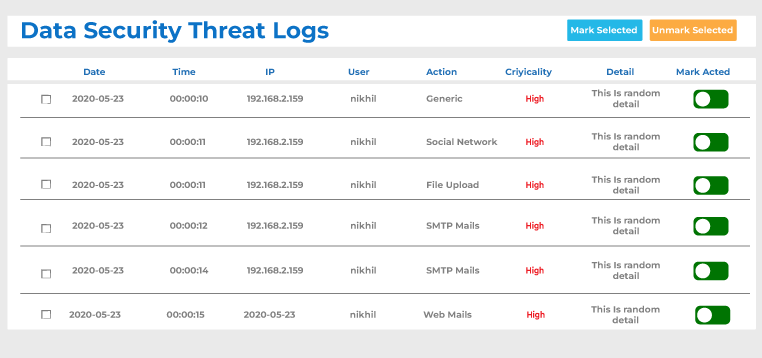
Data Security Threat Plane
See Every Threat VectorExpand your visibility into understanding and identifying each data threat vector by source — for both internal and external communication — and control these threat channels effectively. |
|
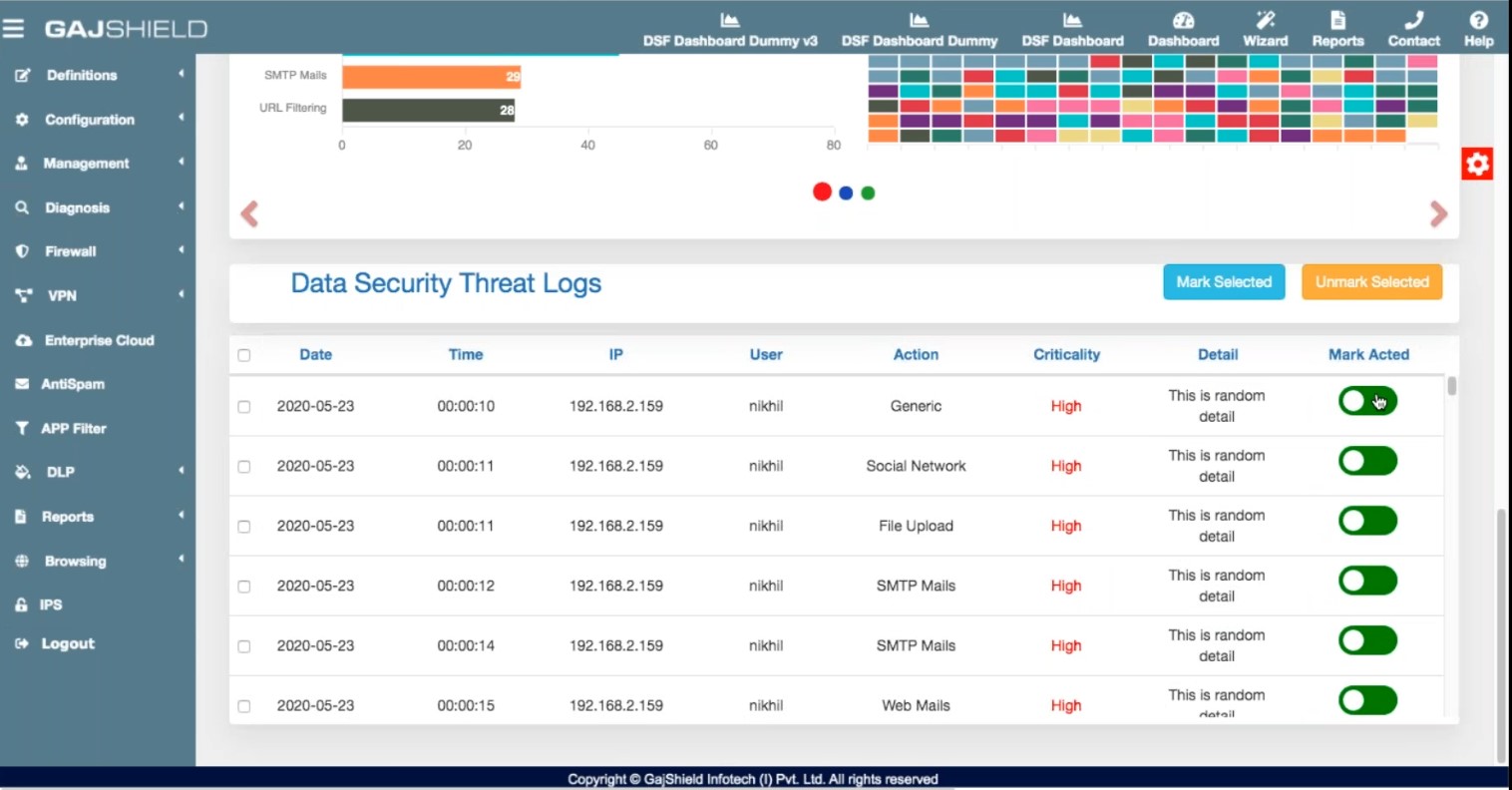
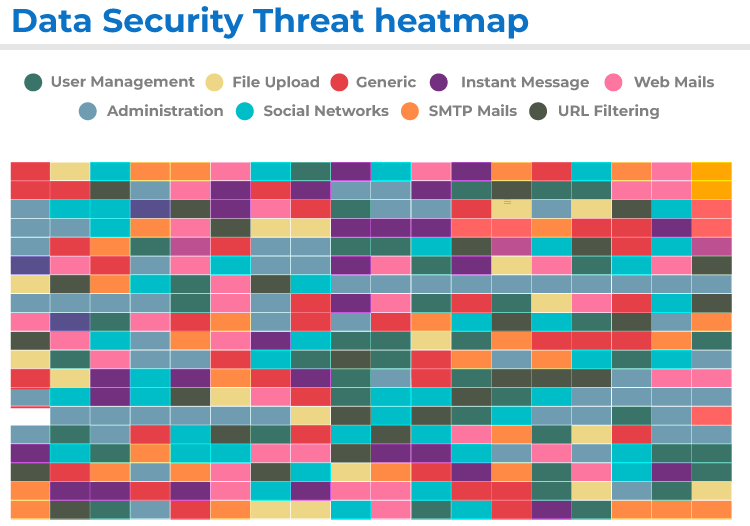
Threat Categories & Heatmap
Identify Patterns As They EmergeMulti-category threat identification for drilled-down data security management. The heatmap surfaces threat patterns in real time so you can take immediate action on abnormalities within your organisation. |
|
|
Quick Threat Response
Take Action From the DashboardRespond to threats directly from the dashboard — no context switching, no additional tools. Improve your overall Data Security Health with one-click protective actions against identified threats. |
One Platform, Every Security Solution
A powerful, robust platform accommodating every security solution needed to prevent data exploitation — powered by GajOS Bulwark and backed by the Contextual Intelligence Engine.
Advanced Data ProtectionTwo-stage protection using machine learning and UEBA to identify suspicious traffic, backed by intelligent sandboxing that simulates human actions to trap malware attempting to steal data. Learn more → |

Contextual Intelligence EngineThe base technology for the Data Security Firewall. Breaks down data packets into multiple contexts for advanced visibility and granular policy decisions. Know more → |

SD-WANSecure interbranch connectivity with centralised policy management, flexible deployment, and consolidated threat visibility — purpose-built for distributed enterprises. Read more → |
Data Leak PreventionEnforcers of data security policies — a centralised framework detecting and preventing unauthorised transmission of confidential information right at the gateway. Know more → |
Enterprise CloudRoute roaming users' network activities through your HO firewall. Apply all firewall policies to browsing and network activity — complete visibility and control for distributed teams. Know more → |
Threat FilteringAdvanced filtering powered by GajShield Threat Labs. Profiles web applications and URL traffic, neutralising malicious attempts right at the gateway before they reach your data. Learn more → |
Zero Trust NetworkTrust none, always verify. Eliminates data breach risk by identifying and authenticating users through multiple policies and methods — preventing lateral movement and unauthorised access. Learn more → |
All Solutions Included
Every GajShield Firewall Ships With the Full StackNo additional licensing, no add-on modules — complete data security from a single appliance. Talk to an Expert → |
|
Seven Pillars of Data Security
What you get when the firewall actually understands your data.

Data Security HealthMonitor overall data security health based on criticality parameters across the organisation. Know more → |

Threat Surface ManagementManage the data threat surface with a two-stage threat categorisation for effective identification. Know more → |

Advanced Data ClassificationBreak down packets into multiple data points using the Contextual Intelligence Engine for better security. Know more → |

SaaS Data ControlControl file uploads and sharing via Gmail, Google Drive, OneDrive, and other SaaS apps — by type, size, and content. Know more → |

Data Visibility & ControlDeep-dive into the data context of every transaction. Log, monitor, and control data usage across web, SaaS, and social media. Know more → |
Security for Roaming UsersSecure remote users by bringing them under the firewall. Apply data security policies and gain full visibility into internet activity. Know more → |
Context-Sensitive DLPUse Contextual Intelligence Engine data to prevent intentional and unintentional data leaks at the network edge. Know more → |
Social & Collaborative App ControlRestrict personal logins of social media and business applications based on business IDs — prevent non-business or illicit use of collaborative tools. Know more → |
|
|
Why Upgrade
Next-Gen Firewalls Don't See DataThe Data Security Firewall uses a Data First Approach. Deep dive into data context, enforce Data Security Policies across cloud and SaaS applications, and take appropriate measures — coverage no NGFW can match. Self-learning. Analyses data patterns and user behaviour to identify anomalies and internal threats. Intelligent packet filtering across local apps, cloud, and SaaS. Explore the Difference → |
|
A Full Range for Every Environment
From GS 20nu to GS 1360nu — GajShield appliances deliver the highest levels of performance and security for SOHO, SME, enterprise, and data centre deployments.

|
Each GajShield Firewall is evaluated against — and has passed — ICSA Labs Modular Firewall Product Certification (Criteria version 4.1x) for general-purpose network firewalls, corporate category. Every appliance is architected for high throughput with multiple solutions deployed simultaneously. Deep Inspection Engine, backed by Contextual Intelligence Engine, classifies network applications and their contextual data in real time. Each appliance supports Active-Active or Active-Passive High Availability, with multiple firewalls manageable through GajShield's Centralized Management System (CMS). |
Built for Every Deployment Environment

Head Office
|

Branch Office
|

Data Center
|

Small Office
|

Factory
|

Virtual Network
|
Ready to Upgrade to a Data Security Firewall?
Talk to a GajShield security expert. We will review your current firewall deployment and demonstrate exactly what your next-generation firewall is missing.
Request a Demo Download Brochure ↓ Become a Partner