|
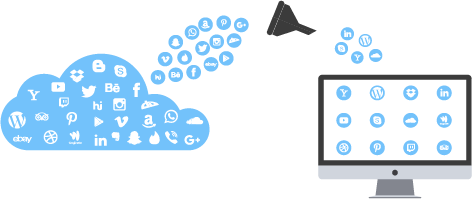
Application Filtering
Control What Apps Actually Run on Your NetworkThe industry's most powerful Deep Packet Inspection engine. Real-time Layer-7 classification of network application traffic with 5000+ application signatures — identifying applications even when they hide inside SSL or standard ports. Request a Demo Explore the Firewall |
|
|
5000+
Application Signatures
|
2,500+
Applications Controlled
|
Layer-7
Real-Time DPI Engine
|
Last-Generation Firewalls Are Blind to Modern Apps
Bandwidth demand is increasing. Web 2.0 architectures changed how protocols are used and data is transferred. Most communication now goes through standard protocols like HTTP and HTTPS — which means traditional firewalls relying on port-based filtering can no longer provide enterprise security.
Many applications use standard ports like 443 to camouflage their traffic. Some, like BitTorrent, can run on any port and hide inside SSL. The strength of a firewall in classifying these applications forms the basis of your network security.
Three Risks of Letting Risky Apps Run Free
While some applications are useful for business, others — like torrents and proxy applications — carry serious consequences if allowed.
|
Risk 1 · Malware
Common Source of InfectionTorrents are common sources of malware and viruses — especially software and games that must be installed and executed. Could lead to network infection and data leak risk through downloaded applications. |
Risk 2 · Legal Liability
Copyright InfringementIf employees torrent illegally on the corporate network — knowingly or not — the organisation could face copyright infringement claims and associated legal liability. |
Risk 3 · ISP Action
Throttling, Fines, SuspensionISPs working with copyright holders monitor traffic. If they catch a customer torrenting, they may resort to bandwidth throttling, fines, or even account suspension — causing business disruption. |
Deeper Than Layer 7
GajShield's Application Filter is the industry's most powerful Deep Packet Inspection engine, providing real-time Layer-7 classification of all network application traffic — including DNS, FTP, HTTP, HTTPS, ICMP, MGCP, NetBIOS Name Service, SMTP, and TFTP — with 5000+ application signatures.
Smart classification examines the data part (and where needed, the header) of every packet at the Application Layer of the OSI model — searching for protocol non-compliance, viruses, spam, intrusions, or defined criteria. This is computer network packet filtering working at depths most NGFWs don't reach.
Beyond Layer-7, the Data Security Firewall offers application and data context visibility — preventing data leakage and sophisticated application-layer threats including malware, phishing, and botnets. Real-time logs and reports let security teams adjust network settings on the fly for maximum security and productivity.
IdentifyDetect 2,500+ applications regardless of port, protocol, or SSL camouflage. |
ClassifySub-classify within categories — allow business apps, block personal accounts of the same service. |
ControlAllow, block, or rate-limit per user, group, IP, network — with full audit trail. |
|
SSL & Encrypted Apps
Detect Apps Hiding Inside SSLModern applications increasingly hide inside SSL or use standard ports like 443 to camouflage their traffic. Port-based filtering can't see them. Identifying applications from SSL protocols and then filtering them is one of the hardest problems in modern firewalling. BitTorrent is a prime example — it can run on any port and wrap inside SSL, making it nearly impossible for traditional firewalls to detect. GajShield's protocol decoding with context-based deep packet inspection blocks traffic based on its actual type, not its port. Talk to an Expert → |
443
The Port Where Apps Hide
"Port 443 is the new wild west. Nearly every modern application disguises itself behind SSL on standard ports. If your firewall only sees port numbers, you're flying blind." |
What You Can Configure & Control
Every Application Filtering capability available in the GajShield platform — organised into four functional groups.
|
VISIBILITY & CONTROL
Application & Data Layer Control
|
POLICY & ENFORCEMENT
Granular Policy Control
|
|
PERFORMANCE & ECONOMICS
Bandwidth & Cost Optimisation
|
SECURITY & PROTECTION
Threat Mitigation
|
See What's Actually Running on Your Network
Talk to a GajShield expert. We will demonstrate Application Filtering on live traffic from your own network — you see exactly which applications are running, on which ports, by which users. Most customers are surprised by what they find.
Request a Demo See URL Filtering See the Full Firewall