|
Data Leak Prevention · Patented Technology
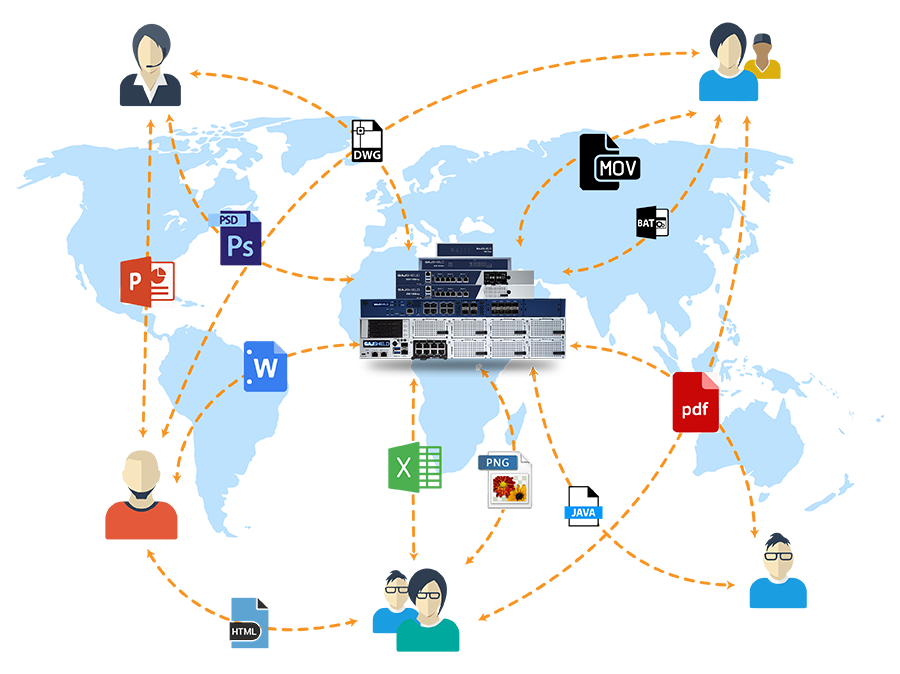
A Unique Context-Based Network DLPThe Data Leak Prevention Solution is an integral part of GajShield's Data Security Firewall — identifying, monitoring, logging, and preventing the misuse and exploitation of data through deep content inspection and contextual security analysis of every transaction. Download DLP Brochure ↓ Request a Demo |
|
|
Context-Sensitive DLP Technology
|
Agentless
Zero Endpoint Footprint
|
Built Into
Every GajShield Firewall
|
Data Leaks Don't Just Happen to Other People
Most policy violations and information breaches are accidental — an inadvertent forward, an attached file with confidential data, an upload to personal cloud storage. These are the words of real GajShield customers describing the data leak risks they couldn't solve before:
|
Loss of Sensitive Information
"I don't know how we can control data from being sent in email or uploaded to the Web." |
Inadvertent Misuse
"Most of our policy violations and information breaches are accidental!" |
|
Collaboration Risk
"I think some of my employees are posting and sharing confidential information on social networking sites." |
Context-Insensitive DLP
"My current DLP causes a lot of false positives and blocks data because it can't understand the web application." |
|
In-Depth Visibility
"Need in-depth visibility on the sensitive data my employees are uploading — in a readable format." |
Roaming Users
"What happens when employees carry laptops while travelling? I need to control leaks even when they're out of office." |
|
68%
of data leaks
|
Happen Through Web and EmailThe two channels every employee uses every day are the two channels you have the least visibility into. GajShield's context-sensitive DLP closes that gap — inspecting the actual data inside web traffic and email, not just the application. |
Eight Pillars of Context-Sensitive DLP
Every capability the original page describes — restructured into a clear capability framework. Each card explains a different way GajShield prevents data leak.
|
01
Deep Inspection of Application DataGoes a layer deeper than application context using the Contextual Intelligence Engine. Inspects email parameters like 'From', 'To', 'Subject', body, attachments — and equivalent contexts for SaaS applications. Granular policy enforcement at the data level, not just port or application. |
02
Inflow & Outflow ControlComplete control over what enters and leaves your network. Set policies to allow or block specific content from being sent out or downloaded — controlling both inflow and outflow of sensitive data with a single policy framework. |
|
03
Context-Sensitive Content InspectionDefine DLP policies based on textual content inside the file. Block files containing keywords like "tenders", "Quotation", or any custom-defined sensitive terms. Deep Packet Inspection scans content in emails, file-sharing uploads, and social media posts — not just file metadata. |
04
File Type, Extension & Content FilteringIdentify and control files by type, extension, and content. Block specific file formats from being uploaded or downloaded. Set size limits on attachments. Allow only document files, restrict executables — complete administrative control over what crosses your perimeter. |
|
05
SaaS & Cloud Application ProtectionGajShield's CASB (Cloud Access Security Broker) ensures all communication between on-premise devices and cloud applications complies with security policies. Block uploads to Dropbox, Google Drive, OneDrive. Inspect file sharing across G-Suite, Office 365, and other cloud platforms in real time. |
06
Roaming User ProtectionA roaming user out of the office is a major data leak vector. Combined with Enterprise Cloud, all communication from off-network devices routes through your HO firewall — protecting against intentional and unintentional data leak even when employees travel. |
|
07
Personal Use RestrictionBlock personal email and social media logins, allow only corporate accounts. Goes beyond traditional website-blocking — allows legitimate use of useful applications while restricting non-business activity. Read-only access policies for corporate webmail and social networking. |
08
Encrypted Traffic VisibilityComplete visibility into HTTPS traffic. SSL inspection for both web and email (SMTP SSL/TLS & STARTTLS). The encrypted channel that traditional DLP can't see is exactly where data leak attempts often hide — GajShield decrypts, inspects, and re-encrypts in real time. |
See What Your Network Was Hiding
Detailed, readable logs of every data transaction — uploads, emails, social media activity. The visibility customers say they need most.
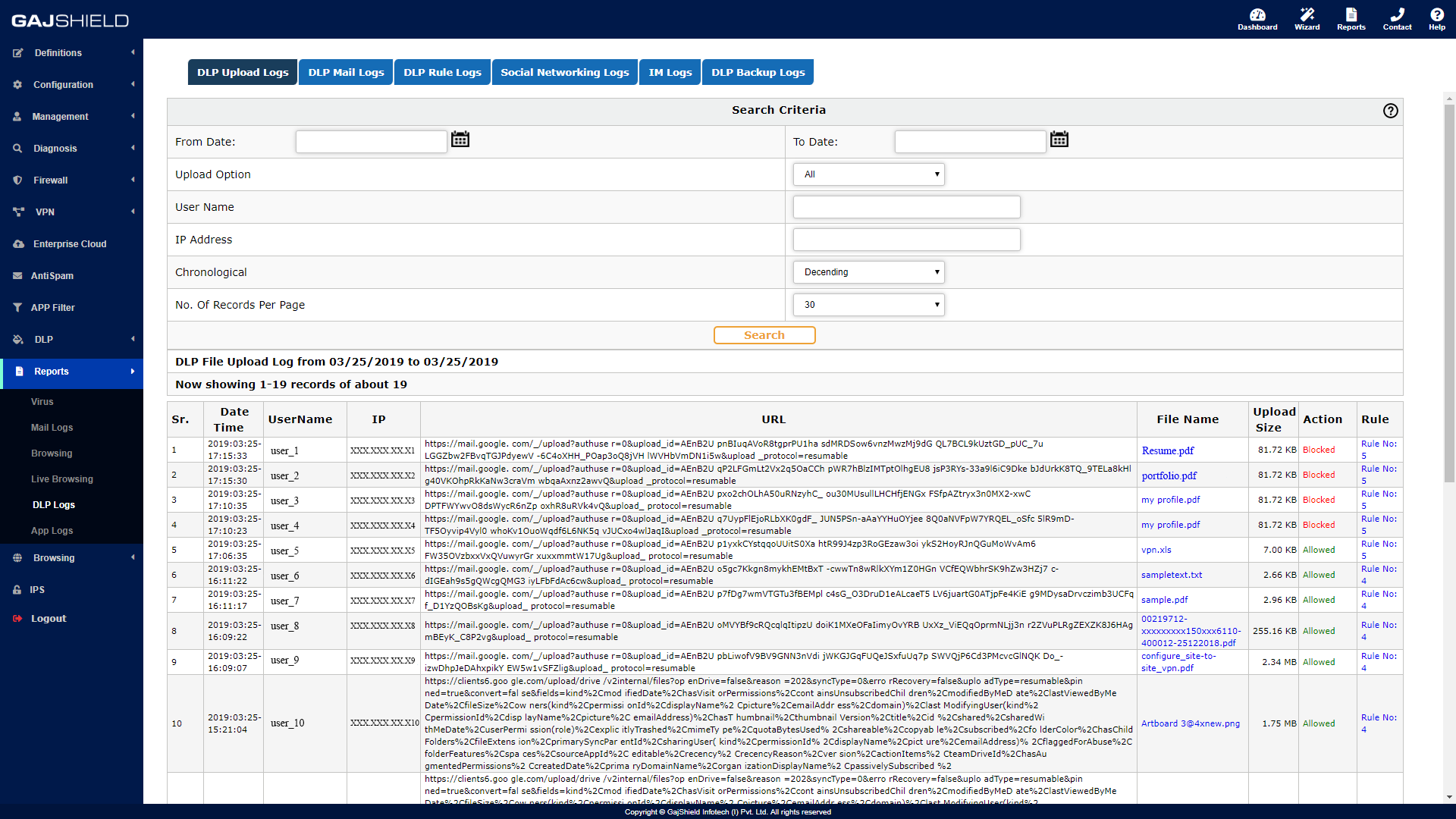
Upload Logs
Every File Upload, Logged |
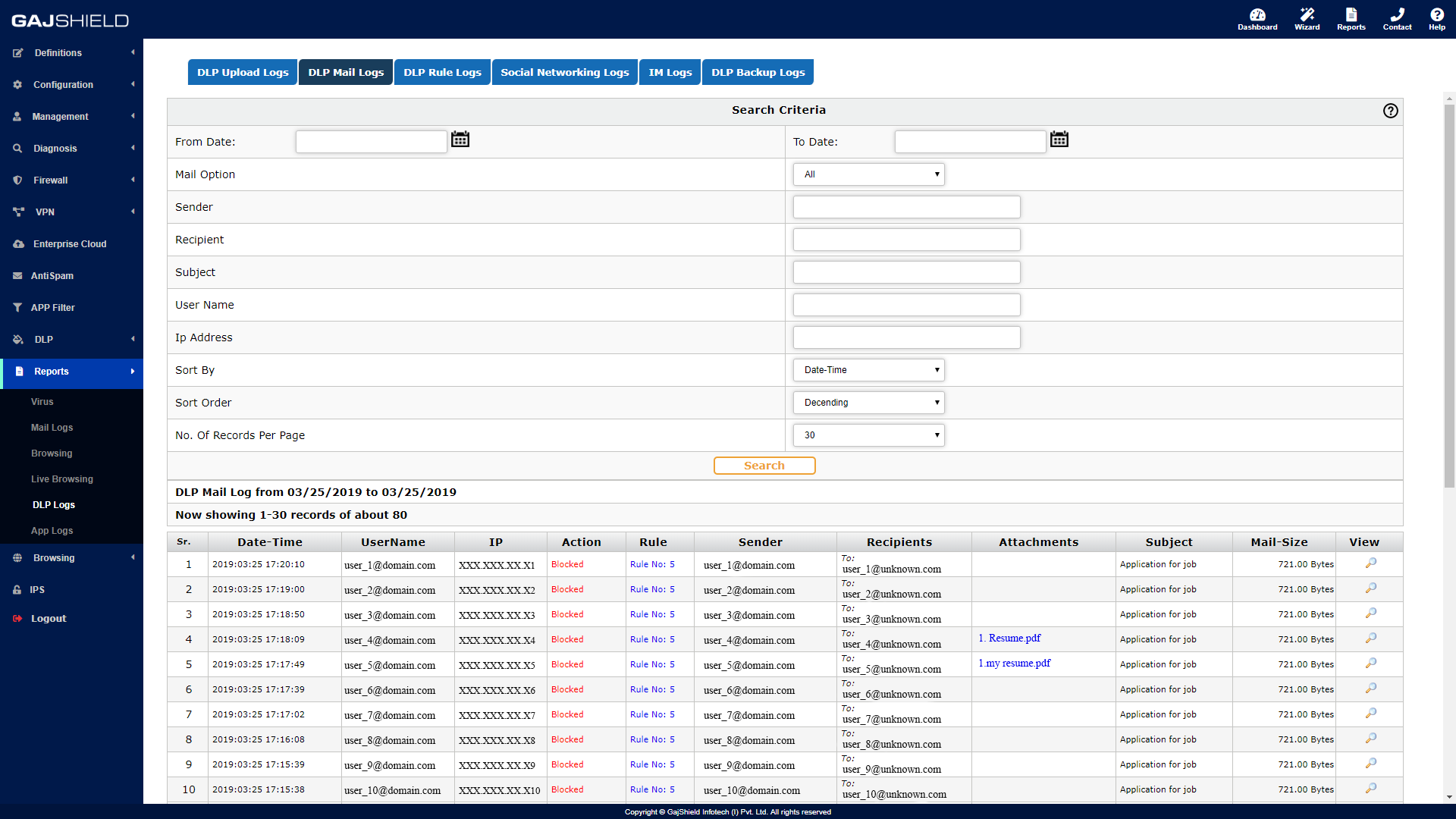
Mail Logs
Email Inspection in Detail |
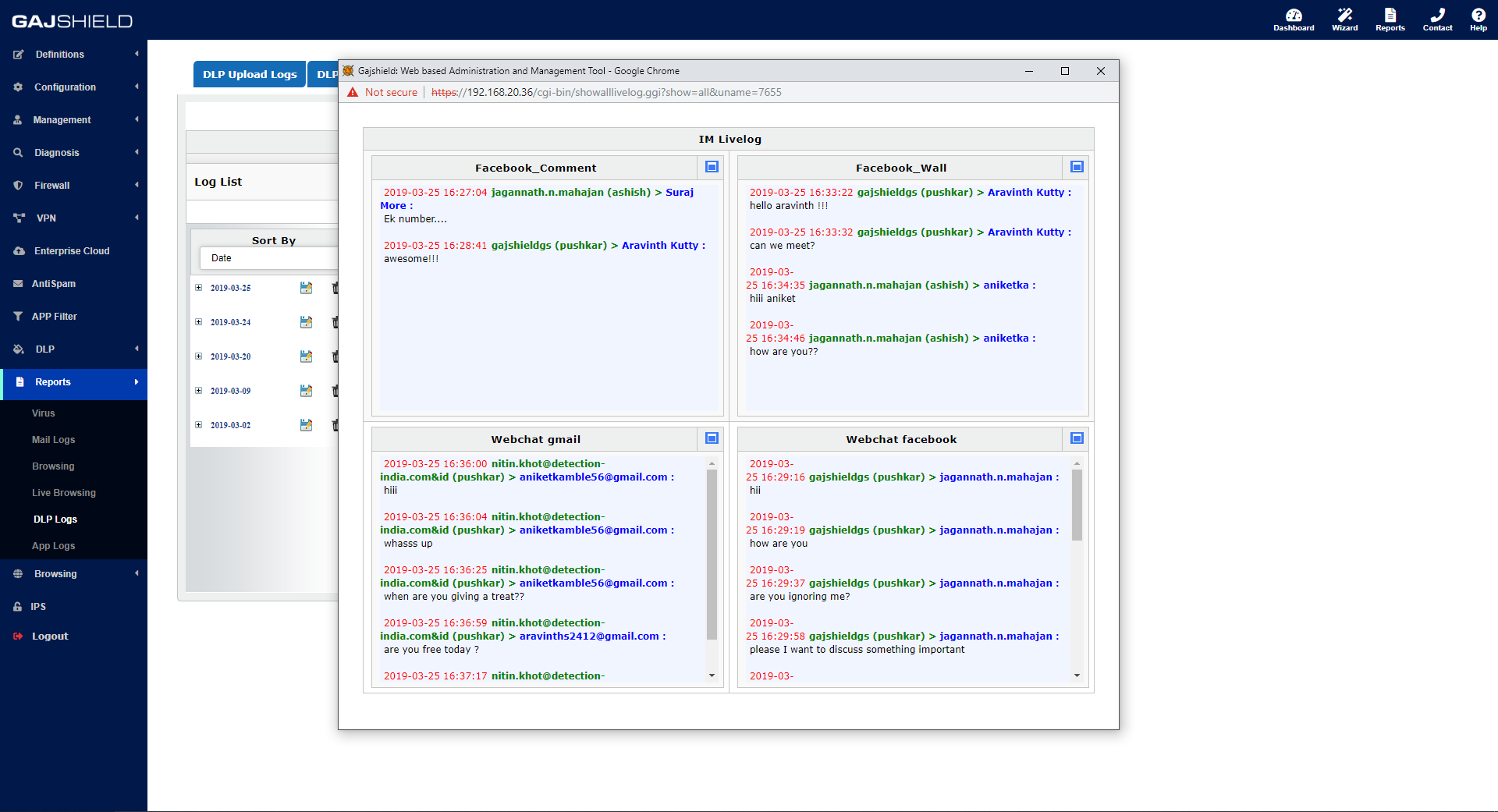
Social Media Logs
Chats, Posts, Comments |
What You Can Configure & Control
Every DLP capability available in the GajShield platform — for evaluators, partners, and compliance teams who need the full feature picture.
Detection & Visibility
|
Policy & Enforcement
|
SSL & Encrypted Traffic
|
Application Coverage
|
Operations & Configuration
|
CASB Capabilities
|
Real Questions, Real Answers
The questions GajShield's sales engineers actually get from prospects evaluating DLP.
Can I block personal email logins and allow only corporate logins?
Yes. Set policies wherein users are allowed only corporate logins. Personal login attempts will be blocked.
Can DLP provide read-only access to webmail (no outbound sending)?
Yes. Security managers can set policies to allow read-only access to corporate emails and social networking platforms.
Can I block emails not CC'd to the head of department?
Yes. Set up policies based on "From", "To", "CC", "BCC", and subject of Gmail and other cloud applications. GajShield also provides BYOD (device) and UserSense (user) information for additional context.
Can I restrict outbound files to only document formats?
Yes. Easily set restrictions on file types allowed to be sent. If a restricted file is sent, an administrator notification fires with full visibility into the file being sent.
Can I monitor employees' Facebook chats and comments?
Yes. Not just Facebook chats and comments — DLP provides global visibility through comprehensive and flexible reporting across all monitored social platforms.
Can I cap the size of attachments sent out?
Yes. Set a cap on the size of attachments that are sent or attached. Configurable per policy, per user group, or per application.
Does GajShield DLP inspect SSL traffic for web and email?
Yes. GajShield inspects SSL traffic for both web and email — including SMTP SSL/TLS and STARTTLS.
Can GajShield DLP block file uploads to Dropbox or Google Drive?
Yes. Using policies, GajShield's DLP effectively blocks file uploads to Dropbox, Google Drive, OneDrive, and other cloud storage applications.
Download the Complete DLP Brochure
All capabilities, deployment scenarios, and feature reference for your team and procurement reviews.
Download DLP Brochure (PDF) ↓Ready to See What Your Network Is Letting Through?
Talk to a GajShield expert. We will demonstrate context-sensitive DLP on live traffic from your own network — so you see exactly what data is leaving today.
Request a Demo Explore the CIE See the Full Firewall