|
Contextual Intelligence Engine
See Data, Not Just PacketsGajShield's signature technology — deep visibility into data transactions across applications. Goes beyond Layer-7 to inspect what data is moving, who is sending it, where it's going, and whether it should be allowed to leave. Request a Demo Explore the Firewall |

|
"While traditional security systems' primary focus is to prevent the wrong people from accessing critical information, context-based security's focus is to enable the right people to access the right type and the right amount of information in the right situations."
Traditional Firewalls Stop at Layer 7
The Contextual Intelligence Engine is a step ahead from traditional firewall capabilities. Using deep inspection at multiple levels for advanced security, CIE understands the application and its data context. It creates context for SaaS applications and understands their usage — much deeper than just identifying the application.
Combined with Machine Learning, CIE helps find anomalies that signature-based or identity-based controls would miss entirely. The result is a robust security layer that's also flexible and intelligent enough to allow access under the right circumstances — expediting business processes while maintaining confidentiality.
Application Context + Data Context
Layer-7 firewalls see the application. CIE goes further — analysing both the application context and the data context together, so you understand what's actually happening at the transaction level.
|
LEVEL 01
Application LevelWho is using which application, when, how, and from where. Goes beyond identifying that a SaaS application is in use — understands the full picture of who's doing what. 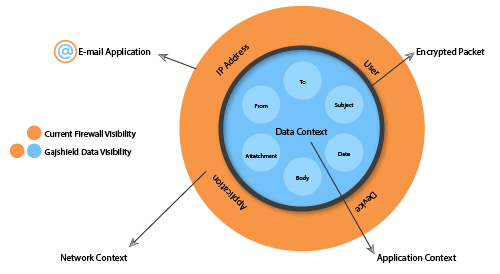
Context Captured
|
LEVEL 02
Data ContextWhat data is moving, who's receiving it, what's inside the message, and what's attached. The crucial layer that turns generic email security into actual data-aware control. 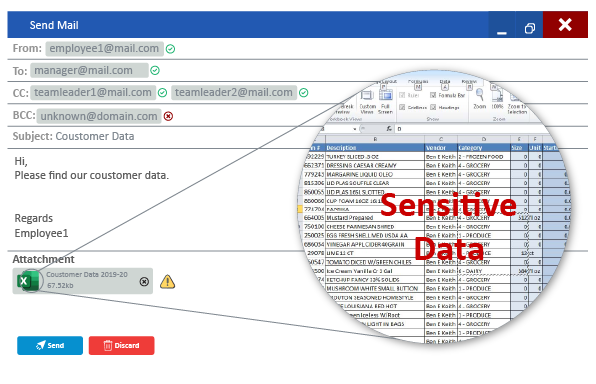
Context Captured
|
SaaS Adoption Made Application Awareness Inadequate
Cloud and SaaS adoption is increasing across every business — allowing employees ease of access to data and services. These businesses need context-intelligent security systems to secure business-critical data without compromising on the convenience of accessing data in exigent situations.
This gives the business a robust security layer that's flexible and intelligent enough to allow access under the right circumstances. Business processes are expedited and performance is enhanced — while the system simultaneously maintains data confidentiality by monitoring abnormal network activity and preventing unauthorised access based on contextual information.
Seven Capabilities Powered by Context
|
01
SaaS VisibilityIncreased visibility on data passing through SaaS applications — not just identifying that the app is in use, but what's actually moving through it. |
02
Advanced Network VisibilityVisibility beyond traditional Layer-7 inspection — understanding the full transaction context, not just protocol identification. |
03
Business-Use EnforcementLimit the use of applications to business use only — allow corporate Gmail, block personal Gmail, even though both are the same application. |
|
04
Mobile Workforce SecurityBetter security for mobile workforce — with the same data context applied whether users are on premises or working remotely. |
05
Roaming User CoverageSeamless security for roaming users — the same data security policies apply to off-network devices as to in-office devices. |
06
Better Gateway SecurityStronger gateway protection by combining application context with data context — catching threats invisible to single-context systems. |
|
07
Endpoint PerformanceUncompromised endpoint performance — CIE runs at the gateway, so endpoint resources stay free for business work, not for security agents. |
CIE + Bulwark
The Three-Layer StackGajShield Bulwark integrates Layer-3 network security, Layer-7 application security, and CIE data context — so a single firewall sees and controls every layer of every transaction. Explore Bulwark → |
|
You Cannot Protect What You Cannot See
It's become a thumb rule for cybersecurity that visibility precedes protection. Cybersecurity is never static — it's an ongoing process that should always be top-of-mind for CSOs, CIOs, and other IT leaders. Security and technology leaders need access to information about the security of their networks at all times. That requires visibility on the network and beyond the network.
Even the most cutting-edge cybersecurity tools cannot keep data protected at all times without visibility. New threats emerge constantly. The time between a threat's incipience and the cybersecurity team becoming aware of it can be the difference between security and enterprise-wide mayhem.
Real-Time Knowledge of Three Things
|
Layer 3 + Layer 7 + Data Context
At GajShield we understand how an enterprise workforce uses data day-to-day, and the importance of that data for business continuity. The data is useful — and if it falls in the wrong hands, the consequences are disastrous. To protect it, you need visibility beyond Layer-7: the contextual data associated with every identified application in use.
GajShield's Data Security Firewall uses the Contextual Intelligence Engine combined with GajOS Bulwark's advanced reporting capabilities to augment traditional Layer-3 (network level) security with Layer-7 (application level) and deeper Data Context — creating real contextual information.
Data Layer inspection extends visibility to email IDs, sender IDs, recipient IDs, CC mentions, subjects, mail bodies, signatures, file content, downloaders, uploaders — across web traffic and SaaS applications. Analysing all these parameters together, the firewall determines the safety and legitimacy of communications and transactions, taking action to prevent data exploitation. This capability is especially useful in mitigating the impact of zero-day attacks.
Visibility, Operationalised
|
APPLICATIONS
Apps & BandwidthComplete visibility of applications in use and bandwidth they consume. Complete visibility of evasive applications like P2P and Skype. |
CONTENT
Outbound Content
|
REPORTING
Trends & AnalysisTrend analysis across applications, users, and bandwidth. Current, daily, monthly, and yearly reports for all activity. |
|
Comprehensive Reporting
Everything CIE Reports On
|
See What Layer-7 Cannot Show You
Talk to a GajShield expert about Contextual Intelligence for your environment. We will demonstrate CIE on live traffic from your own network — you see exactly what data is moving where, who's sending it, and what's inside.
Request a Demo See Bulwark See DLP